If you’ve read even one cautionary tale about the damage that a cybersecurity breach can do, particularly to a business, it’s perfectly natural to feel a little paranoid about the integrity of your machine, your phone, your financial records, and all that data stored on your favorite personal device.
That fear is one of the reasons that scareware – a malware that imitates antivirus software – is so successful. When it infects your device, it fills your screen with warnings that your system is infected by viruses, usually quite a few, or that you are in possession of illegal files and need your system wiped to avoid getting in trouble with law enforcement. Experts estimate that 35 million people have their systems infected with scareware every month.
Scareware is so successful because it plays on most people’s combination of fear of viruses or of getting caught doing something they should not be along with their lack of knowledge about what antivirus software is on any given computer or the difference between real and fake antivirus alerts.
How it Works
Scareware can attach itself to a machine through an email attachment or if a user visits a site infected by it or for the purpose of distributing it. Once active, it launches into “scare mode” by filling a user’s screen with warnings and basically disabling your ability to close the program down. In some advanced versions of scareware, it can pull up images from your computer – particularly if you have visited any risque or adult websites – and will claim that you’re viewing illegal materials and could be reported to law enforcement. It will continually send you messages that you must go to a certain website and buy a cleaner for your computer, which once installed will wipe all of the bad files off your computer.
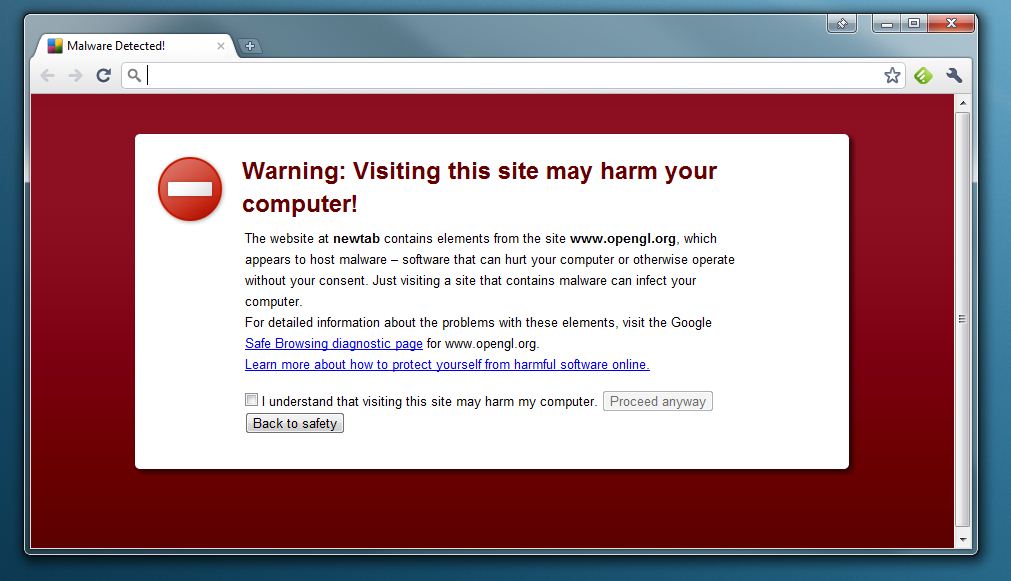
When people buy the cleaner, the malware will run a fake report saying your computer is now clean, even though it never was infected. In some cases, it’s a one-and-done ripoff with the cost of the fake cleaner ranging from $29-$129. In other cases, the form where you enter your credit card information reports it back to wherever the program originated, at which point your credit card is stolen and is used for other purchases until such time as you or your bank put a hold on it or reports it stolen.
How to Avoid It
For starters, use a reputable antivirus software like Bitdefender that you know is trustworthy for the machine you’re using. That way, if you get a message from some other named software, you’ll know it’s a fake and can try the first solution, which is turning your machine off. That might not always work, but it is effective enough to be your first round of defense.
Your second is preventive, in this case not opening any attachments in emails or visiting websites that are suspicious – this includes sites that don’t have a full HTTP address in their links or that don’t have the little “lock” icon next to them in the address bar. With so many ways to send files, including in the cloud or through a service like Dropbox, any attachment should be immediately suspicious. A strong antivirus program installed and updated is also a must-have, as these will usually deter the sort of malware that deploys scareware in the first place.